WordPress File Permissions: The Cornerstone of Digital Security and Operational Integrity

WordPress file permissions are a fundamental, yet often overlooked, aspect of website security and functionality. These granular controls dictate who (or what) can read, write, or execute specific files and directories on a web server, acting as the digital gatekeepers for your entire WordPress installation. Understanding and correctly configuring these permissions is not merely a technical detail for developers; it is a critical security measure that can prevent malicious attacks, data breaches, and severe operational disruptions. When misconfigured, file permissions can either expose a website to significant vulnerabilities, allowing unauthorized access and modification, or conversely, render it inoperable by denying necessary access to core WordPress processes, plugins, and themes. This article delves into the intricacies of WordPress file permissions, their underlying principles, best practices for their management, common pitfalls, and practical methods for adjustment, underscoring their indispensable role in maintaining a robust and secure online presence.
The Unseen Guardians: Why Permissions Matter
At its core, WordPress operates within a server environment, typically a Linux-based system, where every file and directory is assigned specific permissions. These permissions govern how the web server (e.g., Apache, NGINX), WordPress itself, its installed plugins, themes, and various user roles interact with the site’s codebase and content. The importance of these settings cannot be overstated; they form the bedrock of a website’s defensive posture. Without appropriate permissions, even the most robust security plugins or firewalls can be undermined. For instance, if a critical file has overly permissive write access, an attacker who gains even limited entry could potentially inject malicious code, deface the website, or escalate their privileges to compromise the entire server. Conversely, excessively restrictive permissions can lead to a dysfunctional site, manifesting as errors when uploading media, installing updates, or even displaying content, ultimately hindering user experience and business operations.
Cybersecurity reports consistently highlight misconfigurations as a leading cause of data breaches. While a direct timeline of file permission-related incidents is difficult to track specifically, the broader context of web application vulnerabilities frequently points to improper access controls. According to a 2023 report by Sucuri, website compromises remain prevalent, with various attack vectors including outdated software and misconfigurations contributing significantly. File permissions are a silent but constant factor in preventing or enabling these breaches. The principle here is simple: grant only the minimum necessary access. This approach, known as the Principle of Least Privilege (PoLP), is a cornerstone of enterprise security and applies directly to WordPress file management.
Deconstructing File Permissions: The Linux Foundation

To grasp WordPress file permissions fully, one must first understand their origins in Linux/Unix file systems. These systems employ a sophisticated model to control access, which is fundamental to how web servers operate.
Understanding the Triad: Read, Write, Execute
Every file and directory can possess three primary types of permissions:
- Read (r): Allows the viewing of a file’s contents or listing the contents of a directory. For files, it means the ability to open and read. For directories, it means the ability to see what files and subdirectories are inside.
- Write (w): Allows the modification or deletion of a file. For directories, it means the ability to create, delete, or rename files and subdirectories within it.
- Execute (x): Allows a file to be run as a program or script. For directories, it means the ability to traverse into the directory (i.e.,
cdinto it) and access its contents. Without execute permission on a directory, even if read permission is granted, users cannot access the files within.
Defining Access: User, Group, Others
These three permission types are assigned to three distinct categories of entities:
- User (u): The owner of the file or directory, typically the user who created it or the web server user.
- Group (g): A collection of users who share specific access rights to the file or directory. This is often used for team collaboration or by the web server group.
- Others (o): Everyone else on the system who is not the owner and does not belong to the defined group. This category represents the broadest public access.
For each file and directory, you can independently set read, write, and execute permissions for the owner, the group, and others.
Decoding the Language: Symbolic vs. Numeric Notation
File permissions are commonly represented in two ways:
- Symbolic Notation: Uses the letters
r,w,x(or-for no permission) grouped into three sets of three. The first set is for the User, the second for the Group, and the third for Others. For example,rwxr-xr--signifies:- User:
rwx(read, write, execute) - Group:
r-x(read, execute) - Others:
r--(read only)
- User:
- Numeric (Octal) Notation: Assigns a numerical value to each permission:
- Read (r) = 4
- Write (w) = 2
- Execute (x) = 1
- No permission = 0
These values are summed for each category (User, Group, Others) to form a three-digit number. For instance, rwxr-xr-- translates to:
- User: 4 (r) + 2 (w) + 1 (x) = 7
- Group: 4 (r) + 0 (-) + 1 (x) = 5
- Others: 4 (r) + 0 (-) + 0 (-) = 4
Thus, the numeric notation forrwxr-xr--is754. This numeric system is widely used in server administration for its conciseness.
WordPress’s Unique Permission Landscape
While based on standard Linux permissions, WordPress installations have specific requirements due to the dynamic nature of web applications. The web server (e.g., Apache’s www-data user or NGINX’s nginx user) needs appropriate access to process PHP scripts, write to log files, upload media, and manage plugin/theme installations.
Recommended Settings for Core WordPress Files and Directories

Adhering to the Principle of Least Privilege, WordPress has widely accepted standard permission recommendations:
- All Files (General):
644(orrw-r--r--)- The owner (usually the web server user or your hosting account user) can read and write.
- The group and others can only read.
- This prevents arbitrary users or processes from modifying your site’s files.
- All Directories (General):
755(orrwxr-xr-x)- The owner can read, write, and execute (traverse).
- The group and others can read and execute (traverse) but cannot write.
- Execute permission for directories is crucial for the web server to navigate them and access files within.
- The
wp-contentDirectory (anduploadssubdirectory):755(orrwxr-xr-x)- This directory contains themes, plugins, and uploaded media. It requires write access for the web server to handle media uploads, plugin/theme installations, and updates. In some shared hosting environments,
775might be necessary for theuploadsfolder if the web server and your user account are in the same group, but755is generally preferred to limit group write access.
- This directory contains themes, plugins, and uploaded media. It requires write access for the web server to handle media uploads, plugin/theme installations, and updates. In some shared hosting environments,
- The
wp-config.phpFile:640or600(orrw-r-----orrw-------)- This is the most critical file, containing database credentials and other sensitive information.
640: Owner can read/write, group can read, others have no access. This is common if the web server is part of the group.600: Only the owner can read/write, no other access. This is the most secure setting, but might require the web server to be the owner.- Never
644or664or higher forwp-config.phpas it exposes database credentials to other users or even the public, depending on server configuration.
index.php(Root directory):644- Standard file permissions.
The Perils of Misconfiguration: Security Risks and Operational Failures
Incorrect file permissions pose dual threats: they can either open doors for attackers or shut down legitimate site functions.
Vulnerabilities from Lax Permissions
- Malware Injection: If files or directories have
777(full read, write, execute for everyone) or even666(read/write for everyone) permissions, an attacker can easily upload malicious scripts, modify existing core files, or inject code into your database through compromised forms or other vectors. This could lead to a complete site takeover. - Data Theft: Highly permissive
wp-config.phpfiles could allow unauthorized access to database credentials, leading to data exfiltration of user information, content, and sensitive settings. - Website Defacement and SEO Damage: Attackers can alter your site’s content, replacing legitimate pages with spam, phishing attempts, or offensive material. This not only harms your brand reputation but also severely damages your search engine rankings.
- Server Compromise: In the worst-case scenario, overly permissive execute permissions on certain files could allow an attacker to run commands on your server, potentially gaining control over the entire hosting environment and affecting other websites hosted on it.
Disruptions from Overly Restrictive Settings
- Functionality Breakdowns: If WordPress core files or directories lack necessary read/execute permissions, the site may fail to load, display a "White Screen of Death" (WSOD), or show various PHP errors.
- Update and Installation Failures: When
wp-content,plugins, orthemesdirectories lack write permissions, users cannot install new plugins/themes or update existing ones, severely limiting site maintenance and expansion. - Media Upload Problems: Lack of write access to the
wp-content/uploadsdirectory will prevent users from uploading images and other media files, making content creation impossible. - 403 Forbidden Errors: Incorrect directory permissions (e.g., a directory set to
644instead of755) can result in visitors encountering a "403 Forbidden" error when trying to access parts of your site, indicating they lack permission to view the content. - "Error establishing a database connection": While often related to database credentials, overly restrictive permissions on
wp-config.phpcan prevent the web server from reading this crucial file, leading to database connection errors.
Strategic Management: Best Practices for WordPress File Permissions
Managing file permissions requires a cautious and informed approach.
The Principle of Least Privilege in Action
The most critical principle is to grant only the minimum necessary permissions. This means:
- Owner: Typically, the web server user (e.g.,
www-datafor Apache,nginxfor NGINX) should own the files and directories, or at least have full control over them. This prevents other users on a shared server from accessing your files. - Avoid Root Ownership: Granting "root" ownership or
777permissions is almost never necessary for WordPress and dramatically increases security risks. If a hacker exploits a vulnerability, root privileges would allow them to control the entire server, not just your WordPress site. Always ensure that files and directories are owned by the appropriate web server user.
When to Adjust, When to Observe
In most well-configured hosting environments, especially managed WordPress hosting, file permissions are set correctly by default. You should generally avoid changing them unless:
- You encounter a specific error message explicitly mentioning permission issues.
- You are advised by your hosting provider or a trusted security expert.
- You are developing a custom solution that requires specific file access.
Always remember that changing permissions without understanding their implications can cause more harm than good.
The Unforgivable 777: A Security Blunder
Setting any file or directory to 777 grants universal read, write, and execute permissions to everyone. This is akin to leaving your house unlocked with all valuables on display. A savvy attacker can easily exploit this to upload malicious files, modify core WordPress components, or escalate their privileges, leading to a complete compromise of your website and potentially the server it resides on. Despite it sometimes being suggested as a quick fix for errors, 777 is never an acceptable permission setting for a live WordPress site.
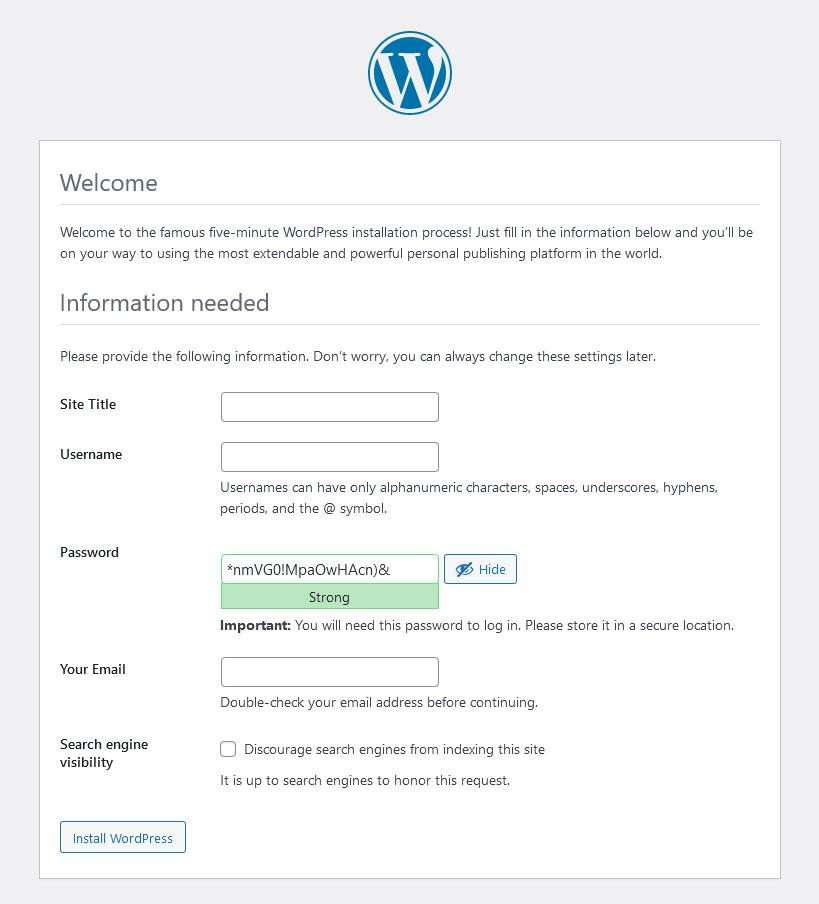
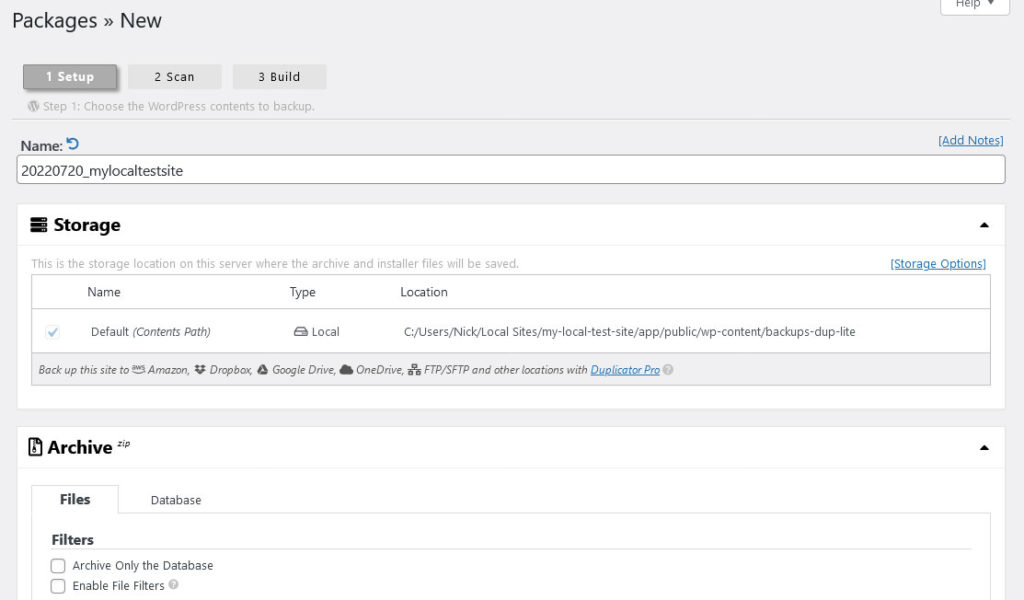
The Indispensable Backup Protocol
Before making any changes to file permissions, or indeed any significant server-level configuration, always perform a full backup of your website and database. This safety net allows you to revert to a working state if an accidental misconfiguration breaks your site. Many hosting providers offer one-click backup solutions, and WordPress backup plugins like UpdraftPlus or Duplicator can also facilitate this crucial step.
Practical Steps: Adjusting WordPress File Permissions
There are several methods to modify file permissions, each suited to different technical comfort levels and hosting setups.
Leveraging Hosting Control Panels (cPanel/Dashboards)
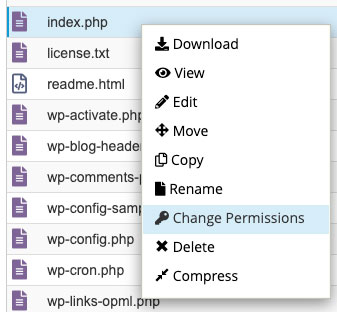
Most web hosting providers offer a control panel (like cPanel, Plesk, or a custom dashboard) with a File Manager. This graphical interface provides a user-friendly way to adjust permissions:
- Navigate to your hosting account’s control panel.
- Find the "File Manager" option.
- Browse to your WordPress installation directory (often
public_html). - Right-click on the desired file or folder.
- Select "Change Permissions" or a similar option.
- Enter the numeric permission value (e.g.,
644,755) or tick the corresponding read/write/execute boxes for User, Group, and Others. - Apply the changes. Some file managers allow you to apply permissions recursively to subdirectories.
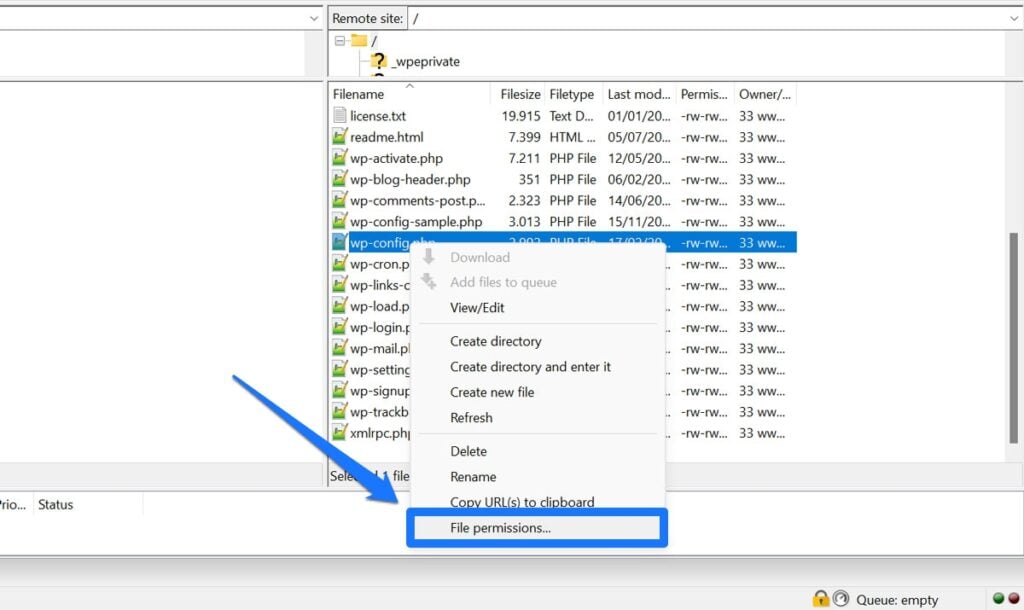
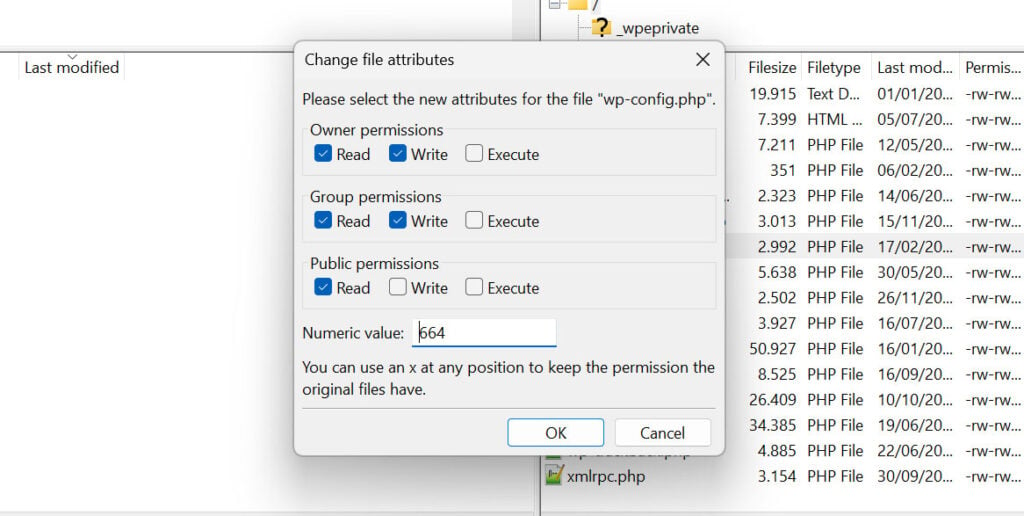
Navigating with FTP/SFTP Clients
For more direct access, an FTP (File Transfer Protocol) or SFTP (SSH File Transfer Protocol) client like FileZilla is a popular choice:
- Download and install an FTP/SFTP client.
- Connect to your web server using the credentials provided by your host.
- Navigate to your WordPress installation.
- Right-click on the file or folder you wish to modify.
- Select "File permissions…" or "Change permissions."
- Enter the numeric value or check the boxes for read, write, and execute for User, Group, and Others.
- For directories, you often have the option to "Recurse into subdirectories" and choose to apply permissions only to directories, only to files, or to both. Exercise extreme caution when using recursive options.
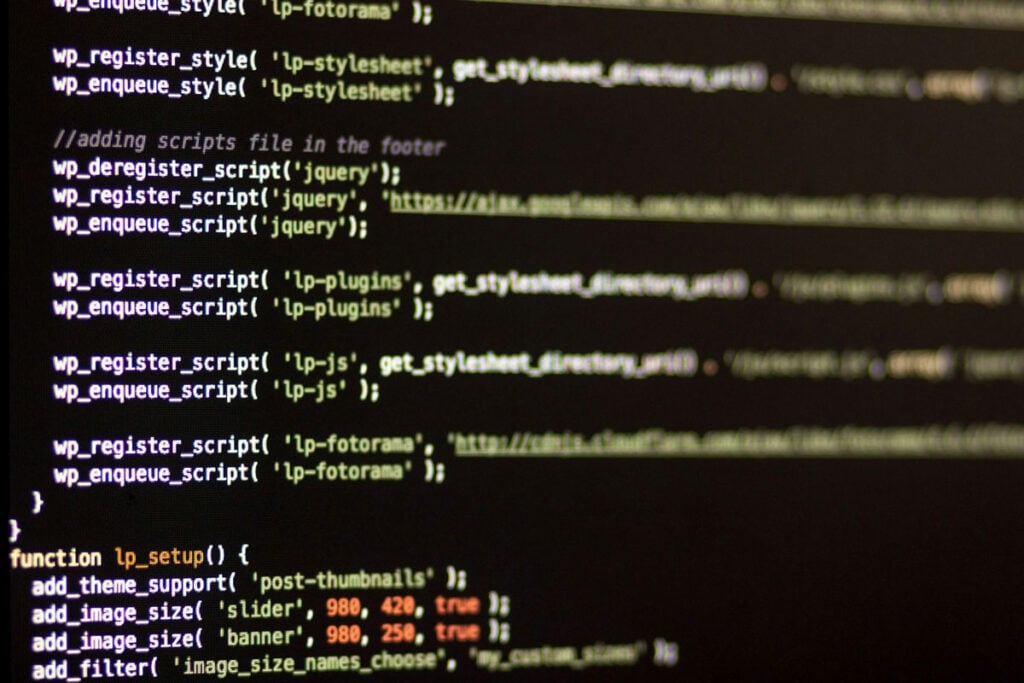
Mastering the Command Line (SSH)
For advanced users, SSH (Secure Shell) access provides the most powerful and precise control over file permissions:
- Connect to your server via SSH using a terminal (macOS/Linux) or PuTTY (Windows).
- Navigate to your WordPress root directory using the
cdcommand (e.g.,cd public_html). - Use the
chmodcommand to change permissions:- To change a file’s permissions:
chmod 644 example.php - To change a directory’s permissions:
chmod 755 example_folder - To recursively set permissions for all files in a directory and its subdirectories to
644:find . -type f -exec chmod 644 ; - To recursively set permissions for all directories in a directory and its subdirectories to
755:find . -type d -exec chmod 755 ; - Caution: Recursive
chmodoperations (chmod -R) are powerful and can easily break your site if used incorrectly. Always double-check your commands.
- To change a file’s permissions:
Simplifying with Security Plugins
Several WordPress security plugins offer features to scan and fix file permissions directly from your dashboard. Plugins like All-In-One Security (AIOS) or Wordfence can:
- Scan your site for insecure file permissions.
- Highlight files or directories with non-standard or dangerous permissions.
- Offer one-click solutions to revert permissions to recommended settings.
While convenient, it’s still advisable to understand what these plugins are doing and to back up your site before initiating automated fixes.
Troubleshooting Common WordPress Permission Errors
When a WordPress site encounters issues, file permissions are often among the first suspects to investigate.
- 403 Forbidden Error: This error message indicates that the server denies access to a requested resource. It frequently occurs when a directory has incorrect permissions (e.g.,
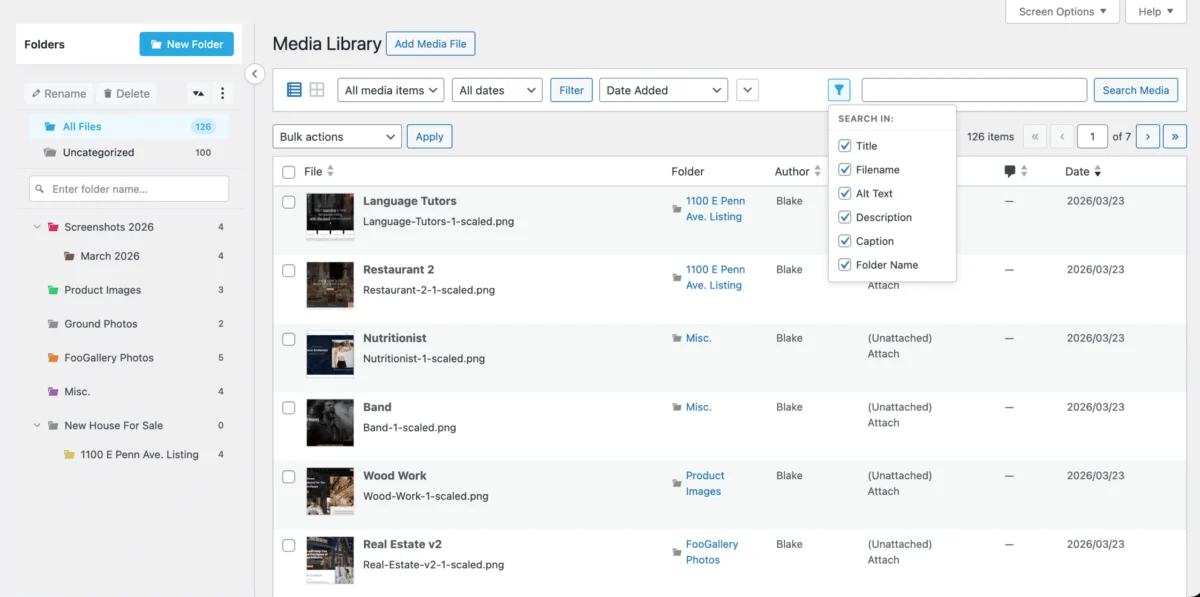
644instead of755), preventing the web server from reading or executing its contents. - Image Upload Failures: If you’re unable to upload images or other media files, it’s highly likely that the
wp-content/uploadsdirectory (or its subdirectories) lacks write permissions. Ensure it’s set to755(or775in specific hosting scenarios). - Plugin/Theme Installation or Update Errors: When WordPress cannot install new plugins/themes or update existing ones, it often points to insufficient write permissions for the
wp-content/plugins,wp-content/themes, or the mainwp-contentdirectories. - "Error establishing a database connection": While typically a database credentials issue, if the
wp-config.phpfile has overly restrictive permissions (e.g.,000), the web server might be unable to read the database connection details, leading to this error. - White Screen of Death (WSOD): A blank white page can have numerous causes, but severely incorrect permissions on core WordPress files or directories, preventing the server from executing PHP scripts or reading necessary files, is a definite possibility.
- Unable to Login to
wp-admin: If thewp-admindirectory or its contained files have incorrect permissions (e.g., missing execute permission for directories or read permission for files), you might be locked out of your administrative area.
Proceed With Caution When Changing WordPress File Permissions
File permissions are a foundational element of WordPress security and operational integrity. While seemingly technical, their correct configuration is paramount to safeguarding your digital assets and ensuring your website functions as intended. The implications of getting them wrong are severe, ranging from critical security vulnerabilities that expose your site to attacks and data breaches, to frustrating operational breakdowns that render your site unusable.
WordPress security experts consistently emphasize the need for a diligent approach to file permissions, advocating for the Principle of Least Privilege and discouraging the use of overly permissive settings like 777. Hosting providers often pre-configure optimal settings, and it is wise to consult their documentation or support channels before making manual adjustments.
Understanding the underlying Linux permission model, the specific needs of WordPress files and directories, and the various methods for adjusting them empowers site administrators to diagnose and resolve issues effectively. However, this power comes with a responsibility for careful execution, always underpinned by comprehensive backups. By treating file permissions with the respect and attention they demand, website owners and administrators can significantly bolster their WordPress site’s security posture and ensure its smooth, uninterrupted operation in the ever-evolving digital landscape.