Decoding WordPress Downtime: Human Error, Configuration Flaws, and the Imperative of Rapid Recovery
Most WordPress outages do not begin with sudden traffic surges or catastrophic infrastructure failures; rather, they typically originate from ordinary, routine changes such as a plugin update, a minor configuration file adjustment, or a small code fix pushed live. This fundamental understanding challenges conventional wisdom regarding website stability and underscores a critical paradigm shift in how digital reliability is perceived and managed. WordPress, a platform renowned for its power and flexibility, inherently relies on human intervention to maintain its smooth operation, meaning that mistakes are an unavoidable component of its lifecycle. Consequently, true reliability is not achieved by eliminating every potential point of failure, but by acknowledging their inevitability and establishing robust mechanisms for rapid identification, safe reversal, and minimal impact when issues arise. This practical approach to reliability is what ultimately defines a resilient online presence.
The Pervasive Role of Human Error in Digital Outages
It is a common misconception that website downtime is predominantly triggered by external forces like overwhelming traffic surges or systemic infrastructure breakdowns. In reality, a significant majority of operational disruptions stem from internal modifications made to the site itself. The dynamic nature of the WordPress ecosystem, characterized by its open-source foundation and extensive library of themes and plugins, ensures a state of perpetual evolution. Plugins are regularly updated, themes undergo adjustments, configurations are refined, and content is continuously edited. Each of these changes, though intended to improve functionality, security, or user experience, simultaneously introduces new variables into the complex system, creating potential points of vulnerability.
This intricate interplay is precisely where seemingly minor human errors can precipitate disproportionately large consequences. A misplaced character in a configuration file, an incompatibility introduced by a routine plugin update, or an unforeseen interaction between components can swiftly render a website inaccessible. Such incidents are neither isolated nor entirely avoidable in the long term; they represent a natural outcome of operating a highly flexible, multi-layered digital platform. Industry reports consistently highlight human error as a significant contributing factor to IT outages across various sectors. For instance, a 2022 Uptime Institute survey indicated that human error remained a primary cause of significant outages for many organizations, emphasizing that even with advanced automation, the human element remains a critical variable. For WordPress, which powers over 43% of all websites globally, the ramifications of such errors can be substantial, affecting businesses, content creators, and millions of end-users. The strategic objective, therefore, shifts from an unattainable goal of total error elimination to a pragmatic focus on effectively managing the fallout when these issues inevitably occur.
Common Vulnerability Points in WordPress Operations
When a WordPress site experiences an issue, the cause is rarely random; instead, failures typically cluster around a few well-defined categories, almost always initiated by small, routine changes.
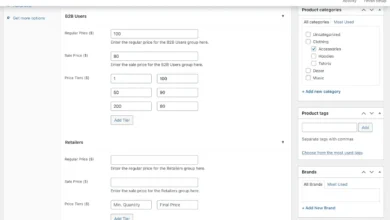
-
Configuration File Errors: At the foundational configuration level, even minute inaccuracies can instantly take a site offline. A classic example is a syntax error within an
.htaccessfile, which is processed by the web server before WordPress even loads. A missing closing bracket or an incorrect directive can trigger a server-level failure, manifesting as a "500 Internal Server Error" – a clear indicator that the server encountered an unexpected condition. Similarly, incorrect database credentials inwp-config.phpcan prevent WordPress from establishing a connection to its database, resulting in the dreaded "Error establishing a database connection." Typos or syntax errors in a theme’sfunctions.phpfile can lead to a "white screen of death," locking out both visitors and administrators from the entire site. These errors are particularly insidious because they halt operations at a very low level, making diagnosis challenging without direct server access or detailed error logs. -
Plugin and Theme Conflicts: The vast and diverse ecosystem of WordPress plugins and themes, while a source of immense functionality, is also a fertile ground for conflicts. Since all components operate within the same execution space, an update to one plugin or theme can unexpectedly interfere with another. A routine plugin update designed to enhance security or add new features might inadvertently break a critical e-commerce checkout flow, disable a site-wide navigation menu, or introduce JavaScript errors that cripple interactive elements. These conflicts often arise from shared library versions, CSS class name clashes, or JavaScript variable overlaps, leading to unpredictable behavior that may not be immediately apparent during initial testing.
-
Editor and Backend Issues: For sites heavily reliant on the block editor (Gutenberg) and JavaScript-driven interfaces, issues can surface specifically within the administrative backend. A script error can prevent the editor from loading correctly, causing controls to disappear or rendering content unsavable. In such scenarios, the frontend of the website might continue to function normally, creating a deceptive sense of stability while content teams are effectively locked out from performing their essential duties, leading to significant productivity losses.
-
Modern Configuration Anomalies (
theme.json): The introduction oftheme.jsonfor block themes and global styles has added another layer of configuration complexity and potential risk. This JSON-based file allows for granular control over typography, colors, layout, and block settings. However, a misplaced key, a duplicated entry, or an invalid structure might not trigger a visible error message. Instead, WordPress may silently ignore parts of the configuration. This subtle failure mode can lead to unexpected styling inconsistencies, missing editor controls, or erratic block behavior across pages, making the root cause significantly harder to trace and debug compared to a glaring 500 error. The lack of explicit error feedback means that issues can persist unnoticed for longer periods, gradually eroding the site’s intended design and functionality.
Each of these scenarios illustrates how WordPress’s dynamic nature, coupled with human interaction, creates numerous vectors for small changes to ripple outwards, causing site-wide instability in ways that are often not immediately obvious.
The Insufficiency of Prevention Alone
The natural organizational response to these inherent risks is to implement more stringent processes. This often involves increased caution with updates, more rigorous review cycles for changes, and the widespread adoption of testing environments before any modifications reach production. While these practices are undeniably crucial for reducing the likelihood of issues and form an essential part of responsible WordPress site management, they do not, and cannot, entirely eliminate the problem.
The underlying reasons for this limitation are multi-faceted. WordPress plugins and themes evolve independently, often developed by different teams with varying coding standards and update cycles. Dependencies between components change over time, and the intricate interactions within a live, complex system are not always perfectly predictable. A change that passes flawlessly in a controlled testing environment might behave differently in production, especially when confronted with real-world data volumes, diverse user traffic patterns, or a unique combination of plugins and themes that were not fully accounted for during the testing phase. Often, issues are not the result of a single, isolated mistake but emerge from the complex interplay of multiple system components under actual operating conditions.
This inherent unpredictability means that even the most meticulous preventative measures cannot offer an absolute guarantee of stability. They significantly lower the probability of something breaking but do not negate the possibility entirely. Backups are frequently regarded as the ultimate fallback, and their importance cannot be overstated. However, merely having backups is only one part of the equation. What holds equal, if not greater, importance is the speed and safety with which those backups can be deployed to restore a site to a known working state when an incident occurs. In some operational environments, restoring a site is a swift, controlled, and automated process. In others, it can involve significant delays, numerous manual steps, or reliance on external support channels, all of which extend the impact duration of the issue and compound the disruption. While these incidents may not be daily occurrences, their impact is rarely minor. A broken checkout process, an inaccessible administrative area, or a site-wide error can halt business operations within minutes, leading to immediate financial losses, damage to brand reputation, and erosion of customer trust. According to various reports, the average cost of downtime can range from thousands to hundreds of thousands of dollars per hour, depending on the size and nature of the business.
Redefining Reliability: Beyond Prevention to Rapid Recovery
Given the inevitability of human error and system complexity, it becomes clear that true reliability in the context of WordPress is not merely about avoiding mistakes, but fundamentally about how the system responds when those mistakes inevitably occur. The pursuit of a website that never breaks is an unrealistic ideal; instead, a site that can recover quickly and predictably from an incident is demonstrably more valuable and practical.
This paradigm shift moves the focus from an unattainable prevention-only mindset to one centered on control and resilience. Instead of solely asking whether a change might introduce risk, the more pertinent and productive question becomes: "How contained is that risk?"
Effective reliability strategies address several key questions: Can an issue be isolated to prevent it from affecting the entire site? Can the problem be identified immediately, or does it languish undetected until users report it? And once identified, can it be reversed swiftly and safely without adding further complexity or stress to an already challenging situation? In practical terms, reliable systems are architected to make failure manageable. This involves implementing rigorous testing of changes in environments that closely mirror production, rather than deploying directly to live sites. When an issue does arise, there must be a clear, well-documented, and rapid pathway to revert to a previous, known working state. Proactive monitoring for issues is paramount, ideally detecting problems before users are even aware of them. The overarching goal is not to eliminate failure, but to ensure that when failures happen, they are contained, quickly resolved, and do not escalate into prolonged downtime or broader operational disruption. This approach aligns with industry best practices that prioritize Mean Time To Recovery (MTTR) as a critical metric for system resilience.
This distinction highlights why two WordPress sites might experience the exact same issue – a problematic plugin update or a configuration error – yet yield entirely different outcomes. One site might recover within minutes with negligible impact, while the other remains unstable for hours or even days as the team navigates manual fixes, protracted restores, or delayed support processes. The initial human error is identical, but the surrounding operational framework and technological infrastructure determine the severity and duration of the disruption.
The Hosting Environment as the Ultimate Safety System
Once reliability is understood as a dual imperative of both prevention and rapid recovery, the strategic importance of the hosting environment comes sharply into focus. The chosen hosting provider and its ecosystem effectively become the overarching safety system, dictating how safely changes can be implemented and how quickly a site can rebound from unforeseen issues.
On the prevention side, a robust hosting environment is designed to minimize unnecessary risk to the live production site. This critically involves providing sophisticated ways to test changes before they go live. Whether it’s a core WordPress update, a new plugin installation, a complex configuration tweak, or the deployment of a new feature, the ability to validate these modifications within a dedicated staging environment is invaluable. A high-quality staging environment should closely mirror the production setup in terms of server configuration, PHP version, and database structure, ensuring that issues caught in staging are genuinely indicative of potential production problems. This capability doesn’t eliminate risk entirely, but it strategically shifts the testing and debugging process into a controlled, isolated space where potential issues can be identified and rectified without impacting live users.
When an incident inevitably occurs, the focus immediately shifts to recovery. This is where the disparities between different hosting environments become most pronounced. In some basic or poorly managed setups, restoring a site can be a laborious, manual process involving multiple steps, often accompanied by uncertainty regarding the exact state the site will return to. This can involve manually uploading database backups, reconfiguring files, and troubleshooting persistent errors. Conversely, a premium hosting environment offers automated, one-click restore points from comprehensive backups, often allowing users to revert to a specific point in time with minimal effort and maximum confidence. This significant gap in recovery speed is frequently the determining factor in whether an issue is perceived as a minor setback or a catastrophic incident. A difference of minutes versus hours or days can have profound financial and reputational consequences for a business.
Furthermore, effective detection plays a pivotal role. If a problem is not immediately visible or reported by users, it can continue to degrade performance, impact SEO, or disrupt user experience for extended periods. Hosting environments that integrate advanced monitoring and alerting systems can proactively surface issues early. These systems monitor server health, application performance metrics, uptime status, and error logs, often notifying teams of problems before they escalate or before users even notice. This early detection capability significantly shortens the "window of impact," allowing teams to respond decisively before the issue proliferates and causes broader damage.
Collectively, these capabilities fundamentally transform how development and operational teams function. Updates, which might otherwise be delayed out of an abundance of caution, can be approached with greater confidence. Mistakes, no longer carrying the existential threat of prolonged downtime, become manageable events because a clear, efficient path to recovery is readily available. A superior hosting environment supports both meticulous change management and rapid correction, creating a sustainable operational framework essential for continuous development and growth in the dynamic digital landscape.
Reliability: The True Measure of Resilience in the Wake of Disruption
Regardless of the experience level of a development team or the meticulousness with which changes are implemented, something will eventually go awry. This is not a failure of process or discipline but an inherent characteristic of operating with a system as constantly evolving and interconnected as WordPress. The distinguishing factor between stable, high-performing websites and fragile, unreliable ones lies not in the absence of problems, but in the efficacy with which those problems are addressed.
When issues can be identified quickly through proactive monitoring, reversed safely via controlled restore points, and contained effectively within isolated environments, they cease to be major incidents and become integrated into the normal rhythm of operations. This strategic approach to managing digital assets is precisely what leading hosting providers like Kinsta are designed to support. Features such as built-in staging environments, automatic and granular backups, and fast, controlled restore points are implemented not merely to keep sites online, but to cultivate an environment of resilience against the everyday changes that are the most common culprits of disruption.
For organizations whose current operational setup renders recovery slow, uncertain, or unduly stressful, it is imperative to re-evaluate not only how the WordPress site is managed internally but, more critically, the underlying system that provides its foundational support. Investing in a hosting environment that prioritizes rapid recovery and robust containment is not merely a technical choice; it is a strategic business decision that underpins continuous operation, preserves brand integrity, and safeguards digital assets against the inevitable challenges of the online world.