Tailored mofu messaging in cybersecurity is a powerful approach to enhance security awareness and engagement. It moves beyond generic warnings, instead delivering personalized messages tailored to specific user groups and threats. Imagine a system that understands individual needs and delivers the right information at the right time, fostering a proactive security culture. This approach not only increases user understanding but also drastically reduces the likelihood of falling prey to sophisticated attacks.
This article explores the concept, methodologies, and practical applications of this approach.
This strategy recognizes that a one-size-fits-all approach to cybersecurity education isn’t effective. By understanding the nuances of different roles, responsibilities, and technical expertise, organizations can create targeted messages that resonate deeply. This personalization improves comprehension and fosters a security-conscious environment, making employees, executives, and customers more resistant to attacks.
Defining Tailored Mofu Messaging in Cybersecurity

Tailored messaging in cybersecurity, often referred to as personalized or segmented messaging, represents a significant shift from generic, one-size-fits-all approaches. This approach acknowledges that different individuals and groups within an organization or user base have varying levels of risk exposure, technical proficiency, and security awareness. By understanding these differences, tailored messages can be more effective in promoting security best practices and reducing vulnerabilities.Tailored Mofu messaging in cybersecurity takes this personalization a step further by focusing on the specific needs and behaviors of individual users or groups.
This goes beyond simple demographic segmentation and delves into understanding individual risk profiles, security knowledge gaps, and past interactions with security communications. This results in messages that are not only more relevant but also more engaging and impactful. Crucially, this targeted approach helps to avoid overwhelming users with irrelevant information, leading to improved reception and retention of security protocols.
Key Characteristics of Tailored Mofu Messaging
Tailored Mofu messaging in cybersecurity distinguishes itself from generic approaches through several key attributes. It leverages data analysis to identify specific user vulnerabilities and tailor security awareness campaigns to address those vulnerabilities directly. This targeted approach focuses on the individual user’s context and environment, increasing the likelihood of successful message reception and engagement.
Target Audience for Tailored Mofu Messaging
The target audience for tailored Mofu messaging encompasses a wide range of individuals and groups within an organization or user base. This includes employees at all levels, contractors, vendors, and even external stakeholders. The effectiveness of these tailored messages hinges on understanding the unique security needs and priorities of each group. A robust approach will also address the varying levels of security awareness and technical knowledge amongst these diverse groups.
Tailored messaging in cybersecurity is crucial, especially for targeted phishing campaigns. Think about how important it is to adapt your approach to different user groups. This is where understanding user behavior becomes paramount. It’s like the Google Penguin algorithm update, which adjusts search results based on factors like website quality and spam. The principle is similar; tailored mofu messaging in cybersecurity requires analyzing individual risk profiles to deliver the most effective and personalized warnings.
This helps prevent breaches and keeps systems secure.
Furthermore, the specific security risks associated with their roles and responsibilities will be factored in.
Comparison of Tailored and Generic Cybersecurity Messaging
The table below highlights the key differences between tailored and generic cybersecurity messaging approaches.
| Characteristic | Generic Cybersecurity Messaging | Tailored Cybersecurity Messaging |
|---|---|---|
| Message Content | Broad, general advice applicable to a wide audience. Often focuses on generic threats and common vulnerabilities. | Specific to the individual or group’s identified risks, knowledge gaps, and behaviors. May include personalized scenarios or examples relevant to the target audience. |
| Delivery Method | Uniform distribution across all recipients. Often through mass emails or announcements. | Targeted delivery based on user segmentation and identified needs. Could involve personalized email campaigns, in-app notifications, or customized training modules. |
| Effectiveness | Lower effectiveness due to potential irrelevance and overwhelming recipients with generic information. | Higher effectiveness due to increased relevance and engagement. |
| Examples | General email about phishing scams, generic security awareness training. | Targeted email campaign about phishing scams for employees in finance department, interactive training modules on password management for newly hired IT staff. |
Methods of Tailored Mofu Messaging
Tailored messaging in cybersecurity, often referred to as Mofu messaging, requires a nuanced approach. It’s not a one-size-fits-all solution; instead, effective Mofu messages are meticulously crafted to resonate with specific user groups and address their unique needs and vulnerabilities. This personalized approach dramatically increases the likelihood of engagement and successful information absorption.Tailored Mofu messaging employs various methods to achieve this personalization.
These methods range from simple adjustments to content and delivery channels to more complex strategies incorporating user behavior analysis. Understanding the strengths and weaknesses of each method is crucial for maximizing the impact of cybersecurity awareness campaigns.
Content Customization
Tailoring the content of Mofu messages is fundamental. This involves adapting the language, tone, and examples used in the message to resonate with the specific user group. For instance, a message aimed at junior employees might use simpler language and relatable examples, while a message targeted at senior management might focus on the financial implications of security breaches.
The key is to speak the language of the audience, ensuring they understand the importance of the message and its relevance to their roles. This method is highly effective in engaging diverse audiences by ensuring the message is easily understood and actionable.
Channel Selection
Choosing the appropriate communication channel is equally critical. Different channels cater to different preferences and habits. A short, concise message delivered via email might be suitable for broad communication, while a more interactive video might be better for reaching younger employees. Social media platforms, instant messaging systems, and even in-app notifications can all be used to disseminate tailored messages, each with its own unique strengths and weaknesses in terms of engagement.
User Segmentation
User segmentation is a powerful method for delivering highly tailored messages. Dividing the user base into smaller, more homogeneous groups based on factors like job role, department, or even risk profile allows for the creation of messages that are highly relevant to the individual. For instance, a message on phishing awareness might be more targeted toward employees who frequently access sensitive data, while another message might focus on the importance of strong passwords for all users.
Dynamic Content Delivery
Dynamic content delivery takes personalization a step further. This method uses real-time data and user behavior to adapt the message on the fly. For example, if an employee frequently clicks on suspicious links, a tailored message reminding them of the dangers of phishing might be automatically displayed. The effectiveness of this method depends on the availability of relevant user data and the ability to integrate it with the messaging system.
Example Table of Methods
| Method | Strengths | Weaknesses |
|---|---|---|
| Content Customization | High relevance, improved understanding, increased engagement | Requires significant effort to tailor for each segment, potentially time-consuming |
| Channel Selection | Enhanced accessibility, caters to user preferences, optimized engagement | Different channels require different content formats, potentially costly for varied deployment |
| User Segmentation | Targeted messaging, improved ROI, reduced redundancy | Requires accurate and up-to-date user data, potential for bias in segmentation |
| Dynamic Content Delivery | Real-time adaptation, proactive engagement, immediate impact | Requires sophisticated systems and data integration, potential for user overload |
Content Creation for Tailored Mofu Messages

Crafting effective Mofu messages in cybersecurity requires a deep understanding of your audience. These messages, delivered through various channels, aim to educate, inform, and ultimately, protect. Tailoring the content to specific user groups, incorporating visuals, and using appropriate language are crucial for successful communication. This approach ensures the message resonates with the recipient and encourages the desired action.Effective tailored Mofu messages are not generic announcements.
They are personalized communications that address the specific concerns and needs of the target audience. This targeted approach maximizes engagement and fosters a proactive security culture. This section details the essential elements of creating compelling and impactful Mofu messages.
Essential Elements of Effective Tailored Mofu Messages
Tailored Mofu messages need to be clear, concise, and actionable. Understanding the audience’s background and priorities is paramount. The language used should be accessible and avoid technical jargon. Focus on clear benefits for the recipient.
Examples of Compelling Content for Different User Groups
For employees, messages should focus on practical steps they can take to mitigate risks. Use real-world scenarios and highlight the consequences of negligence. For executives, emphasize the financial and reputational risks of cyberattacks. Present data and statistics to demonstrate the potential impact. For customers, focus on the security measures in place to protect their data and explain how they can contribute to their own security.
Simple and direct language is crucial for this audience.
Tailoring Message Tone and Language
The tone and language should align with the specific audience. For employees, a supportive and instructive tone is ideal. For executives, a professional and data-driven tone is appropriate. For customers, a reassuring and transparent tone is vital. Avoid using overly technical language in any communication.
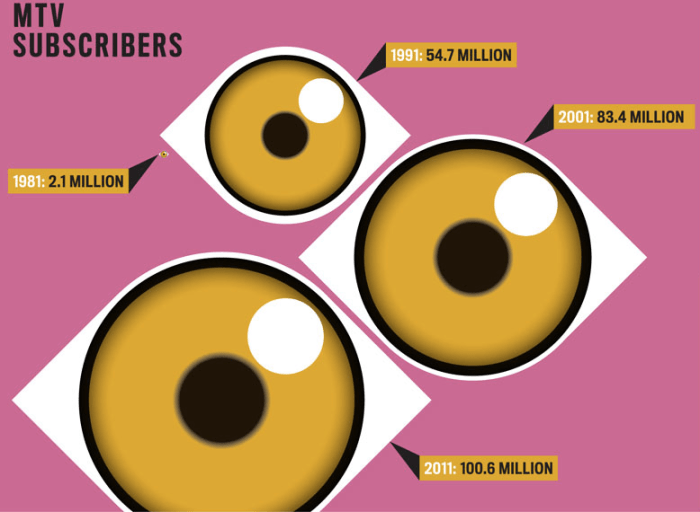
Importance of Visuals and Multimedia
Incorporating visuals and multimedia elements significantly enhances the impact of Mofu messages. Infographics, short videos, and interactive elements can make complex information more engaging and easier to understand. These elements help to break up large blocks of text and capture attention. For example, a short animated video can illustrate the process of a phishing attack more effectively than a lengthy text description.
Best Practices for Message Content by Audience
| Audience | Content Focus | Tone | Visuals | Call to Action |
|---|---|---|---|---|
| Employees | Practical security tips, real-world scenarios, risk mitigation strategies, and consequences of security breaches. | Supportive, instructive, and proactive. | Infographics, short videos demonstrating phishing attempts, interactive quizzes. | Complete a security training module, report suspicious emails, participate in simulated phishing exercises. |
| Executives | Financial and reputational risks of cyberattacks, quantifiable data on security breaches, impact on business operations. | Professional, data-driven, and proactive. | Data visualizations, charts, graphs demonstrating the cost of breaches. | Review the security posture, implement security upgrades, allocate resources to security. |
| Customers | Data security measures, how they can contribute to their own security, clear explanations of security procedures. | Reassuring, transparent, and helpful. | Simple infographics, easy-to-understand diagrams explaining security protocols. | Update account details, report suspicious activity, utilize the provided security resources. |
Implementation and Delivery Strategies: Tailored Mofu Messaging In Cybersecurity
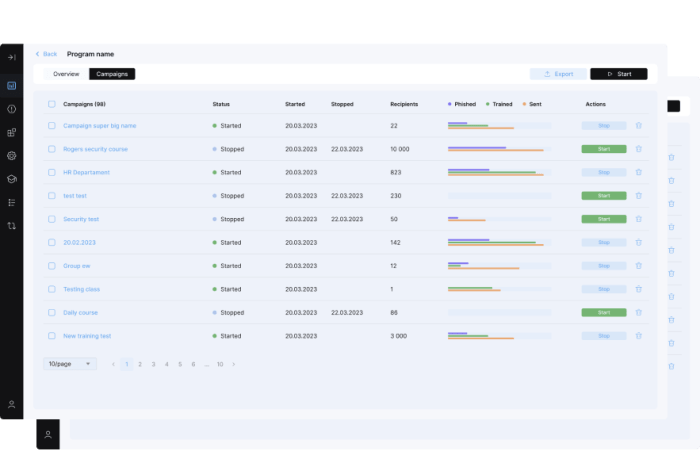
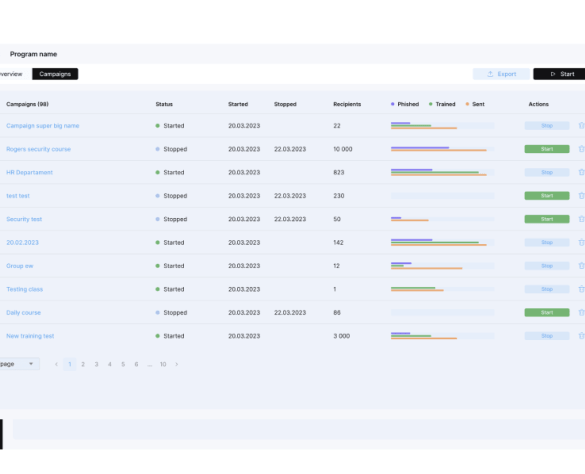
Tailored micro-focused outreach (Mofu) messaging in cybersecurity requires a strategic approach to implementation and delivery. Effective Mofu campaigns aren’t just about crafting the perfect message; they hinge on meticulous planning for how those messages reach the intended audience and integrate seamlessly with existing security infrastructure. This meticulousness ensures maximum impact and minimizes wasted effort.A robust implementation strategy considers the unique needs of each targeted audience segment.
It involves not just the message itself, but also the channel selection, platform integration, and evaluation metrics. This multifaceted approach allows organizations to optimize their resources and achieve their security objectives more efficiently.
Implementation Strategies
Different organizations have varying needs, so a one-size-fits-all approach is ineffective. A tailored implementation strategy is crucial for successful Mofu messaging. To ensure that the messaging aligns with the specific goals and capabilities of each organization, the strategies must be flexible and adaptable. This flexibility is vital to ensure that the messages resonate with the target audience and encourage the desired behavior.
Tailored messaging in cybersecurity, often focused on specific user groups (mofu), is crucial. Thinking about how mobile marketing and 5G are changing the game, mobile marketing and 5G opens new avenues for targeted outreach. Ultimately, this refined approach to mofu messaging in cybersecurity enhances proactive threat detection and response, making systems more secure.
- Phased Rollouts: Begin with a small, controlled group to test and refine the messaging and delivery before scaling up to the entire target audience. This allows for adjustments based on real-time feedback, ensuring maximum impact. For instance, a company might initially target a specific department or team to observe the response rate before expanding to the broader organization.
- Automated Delivery Systems: Leveraging automation tools streamlines the delivery process, allowing for consistent and timely communication. This ensures messages are sent precisely when needed, often triggered by specific events or user behavior. Automated systems are particularly useful for delivering routine security reminders and alerts, maximizing impact and efficiency.
- Integration with Existing Platforms: Seamless integration with existing security information and event management (SIEM) systems, security orchestration, automation, and response (SOAR) tools, and other platforms minimizes manual effort and improves overall efficiency. This integration streamlines the workflow, allowing for quicker responses to threats and more efficient handling of security incidents.
Delivery Channels
Choosing the right channels for delivering tailored Mofu messages is crucial. The channel must be relevant to the audience and consistent with the message’s tone.
- Email Marketing Platforms: Targeted email campaigns can effectively deliver specific messages to different user groups. Emails can be personalized to address individual needs, fostering engagement and increasing the likelihood of a positive response. Examples include targeted security awareness training reminders or updates on recent security vulnerabilities.
- In-App Notifications: Delivering notifications directly within applications used by employees can enhance engagement and awareness, especially for critical alerts or training modules. This approach allows for timely and relevant communication, ensuring prompt action from users.
- Intranet Portals: Intranets can host curated content and information that address specific security concerns or provide tailored training resources. This allows employees to access the information they need, when they need it, fostering proactive security behaviors.
Measuring Effectiveness
Quantifiable metrics are essential to gauge the effectiveness of tailored Mofu messaging.
- Open and Click-Through Rates: Monitoring open and click-through rates for emails and notifications provides insights into message engagement. High rates suggest the message is relevant and interesting, while low rates may signal a need for adjustments to the content or delivery approach.
- User Behavior Analysis: Tracking user behavior after receiving the message, such as participation in training or adherence to security protocols, provides concrete evidence of the message’s impact. This helps evaluate the message’s effectiveness in driving desired security behaviors.
- Security Incident Reduction: Correlation between the implementation of Mofu messaging and a decrease in security incidents provides strong evidence of its effectiveness. This approach is particularly useful in evaluating the long-term impact of the campaign and its contribution to the overall security posture.
Implementation Strategies Table
| Strategy | Platforms | Channels |
|---|---|---|
| Phased Rollouts | Security Information and Event Management (SIEM) systems, Security Orchestration, Automation, and Response (SOAR) platforms | Email, In-App notifications, Intranet portals |
| Automated Delivery Systems | Email marketing platforms, In-app notification systems | Email, In-App notifications |
| Integration with Existing Platforms | SIEM systems, SOAR platforms, Identity and Access Management (IAM) systems | All channels (email, in-app, intranet) |
Mofu Messaging in Different Cybersecurity Scenarios
Tailored messaging, or “Mofu” messaging, isn’t just a buzzword; it’s a powerful tool for bolstering cybersecurity. By personalizing security communications, organizations can significantly improve user engagement and understanding, ultimately leading to a stronger security posture. This approach allows for targeted information delivery, ensuring users receive precisely the right message at the right time, making them more receptive to security advice and procedures.
Preventing Phishing Attacks
Tailored Mofu messages are invaluable in the fight against phishing. Instead of generic warnings about phishing, targeted messages can be sent to specific users based on their past browsing history, login attempts, or even their role within the organization. For example, a user frequently visiting suspicious financial websites might receive a personalized message highlighting the risks of phishing attempts targeting financial accounts.
This proactive approach is more effective than a broadcasted message, as it addresses individual risk profiles. This personalized approach can also educate users about the specific types of phishing attempts they are most susceptible to, equipping them with the knowledge to recognize and avoid them.
Incident Response and Recovery
In the event of a cybersecurity incident, tailored Mofu messaging plays a crucial role in incident response and recovery. Real-time updates and instructions, customized to the user’s role and access level, can be sent to minimize disruption and ensure a swift recovery. For instance, during a ransomware attack, employees with administrative privileges might receive immediate instructions on how to isolate affected systems, while others might receive information on data backup procedures.
This targeted approach ensures that the right information reaches the right people at the right time, streamlining the recovery process and minimizing damage.
Improving User Awareness and Security Culture
Security awareness training is significantly enhanced by tailored Mofu messaging. Regular, targeted messages can reinforce security best practices, like strong password creation and safe internet browsing. For instance, a user who has recently changed their password might receive a message reinforcing the importance of strong passwords and providing resources to help them create more secure ones. This reinforces a positive security culture, where users are actively involved in protecting the organization’s digital assets.
A positive security culture will lead to less vulnerabilities and better incident response.
| Cybersecurity Scenario | Tailored Mofu Messaging Application |
|---|---|
| Phishing Prevention | Personalized messages based on user behavior and risk profile, highlighting specific threats. |
| Incident Response | Real-time updates and instructions customized to user roles and access levels. |
| Security Awareness Training | Regular, targeted messages reinforcing best practices and providing resources for improvement. |
Illustrative Examples of Tailored Messages
Tailored messaging in cybersecurity is about delivering the right information to the right people at the right time. Instead of generic alerts, this approach personalizes the message to resonate with the recipient’s role, responsibilities, and potential vulnerabilities. This significantly increases the likelihood of engagement and action.Effective tailored messages go beyond just stating the problem; they aim to create a sense of urgency and relevance by weaving in real-world examples.
This is crucial for fostering a proactive security culture.
Examples for Phishing Attacks
Tailored phishing messages should be highly specific to avoid looking suspicious. Generic messages are easily flagged by modern email filters and often get ignored.
“Dear [Employee Name], We’ve detected unusual activity on your account. Please verify your login credentials by clicking this link [malicious link].”
Tailored messaging in cybersecurity, or “mofu” messaging as it’s sometimes called, is crucial for protecting your business. Understanding your partners’ needs is key to effective communication, and that includes knowing how to protect business marketing partners. Following protect business marketing partner tips can help you ensure everyone is on the same page, reducing the risk of breaches and other security issues.
This tailored approach, focusing on specific vulnerabilities and threats, is a vital component of a strong security posture for any business.
This example, while technically a phishing attempt, is not tailored. A tailored message would include specific details about the suspicious activity, linking it to the employee’s recent work.
“Dear [Employee Name], We noticed unusual activity from your account. You recently accessed a document requiring specific security protocols. To avoid any disruption, please verify your account credentials by clicking the link below: [link to a legitimate, company-issued login page].”
This example illustrates a tailored approach. It mentions the employee’s recent actions and redirects them to a legitimate login page, thus increasing the chance of avoiding a phishing attack.
Examples for Malware Infections
Tailored messages for malware infections should be targeted to the specific type of malware and the likely impact on the user. It is crucial to avoid sounding alarmist, and instead, use a tone of concern and helpfulness.
“Dear [Employee Name], Your workstation has been flagged for potential malware infection. Please proceed to [link to company’s support page] for further assistance. Our IT department will assist you in removing the malware and restoring your files.”
This example is generic and lacks tailored specifics. A better approach would be to include information about the specific symptoms the user has experienced.
“Dear [Employee Name], We’ve detected a known ransomware infection on your workstation, and your access to [specific file type or application] has been temporarily restricted. Please contact our IT support immediately for guidance on restoring your data and preventing further damage. We are committed to minimizing any disruption.”
This tailored message specifies the type of malware, the impact on the user’s work, and the next steps, creating a sense of urgency and support.
Adapting for Different Technical Expertise
Messages must be adaptable to different levels of technical expertise. Technical jargon should be avoided when addressing non-technical staff.
“Dear [Employee Name], A recent email may contain malware. It’s best to be cautious with unfamiliar emails, and to contact your supervisor or IT support if you are unsure.”
This example is suitable for a non-technical audience. It avoids complex terminology and focuses on the practical steps to take.
“Dear [Employee Name], Analysis of network traffic indicates a potential exploit targeting the vulnerability in our [specific software]. To mitigate the risk, ensure you have the latest security updates installed and report any unusual activity to IT.”
This example targets a more technically savvy audience and includes specific details and actionable steps.
Metrics and Evaluation for Tailored Mofu
Measuring the effectiveness of tailored Mofu messaging in cybersecurity is crucial for optimizing campaigns and maximizing their impact on user behavior. This process involves more than just counting clicks; it necessitates a deep dive into user engagement and the resulting changes in security awareness. Understanding how to track and interpret these metrics will allow for continuous improvement and adaptation of the messaging strategy.
Key Metrics for Evaluating Effectiveness
A comprehensive evaluation of tailored Mofu messaging goes beyond basic click-through rates. It necessitates tracking a range of metrics that reflect the multifaceted nature of user engagement and its impact on security awareness. These metrics should encompass the entire journey from message exposure to a demonstrable change in behavior.
- User Engagement Metrics: These metrics focus on how users interact with the messages. This includes open rates, click-through rates, time spent interacting with the message, and the number of interactions within the message (e.g., clicking on links, watching videos). Tracking these metrics provides insights into the overall appeal and relevance of the message content. High engagement rates indicate that the message is capturing attention and prompting further exploration.
- Security Awareness Metrics: These metrics assess the impact of the message on users’ security awareness. This involves measuring changes in knowledge retention, attitudes towards security risks, and the adoption of new security practices. Surveys, quizzes, or behavioral observations can be used to gauge changes in security awareness.
- Behavioral Change Metrics: This segment assesses the practical impact of the message on user behavior. Metrics include changes in password complexity, the frequency of using multi-factor authentication, and the adoption of security best practices. Tracking these metrics provides evidence of the messaging’s effectiveness in prompting tangible security improvements. For example, a noticeable increase in password strength scores could be a clear indication of a successful campaign.
Defining Key Performance Indicators (KPIs), Tailored mofu messaging in cybersecurity
KPIs are quantifiable metrics that specifically measure the success of the tailored Mofu messaging campaign. They provide concrete benchmarks for evaluating performance and should be aligned with the overall cybersecurity objectives.
- Open Rate: Percentage of users who opened the message. This indicates the initial success in capturing attention.
- Click-Through Rate (CTR): Percentage of users who clicked on a link or call-to-action within the message. This shows the effectiveness of the message in prompting further action.
- Time on Message: Average time spent interacting with the message. A longer duration suggests the message is compelling and informative.
- Survey Score Improvement: Percentage increase in correct answers on security awareness surveys before and after the campaign. This metric demonstrates a rise in knowledge retention.
- Adoption of Security Best Practices: Percentage of users who implemented new security practices after exposure to the campaign. This metric measures the practical impact of the messaging on behavior.
- Reporting Rate of Suspicious Activity: Percentage of users who reported suspicious activity following the campaign. This metric indicates the effectiveness of the message in prompting proactive security behavior.
Interpreting Results and Adjusting Strategy
Analyzing the collected data is critical for understanding the campaign’s success and identifying areas for improvement. Patterns in the metrics will reveal insights into what resonates with the target audience and what needs to be adjusted. A decline in engagement metrics, for instance, might suggest the need for a revised message format or different content. Continuously monitoring and evaluating metrics allows for a dynamic approach to messaging, ensuring it remains relevant and impactful.
| Metric | Description | Target | Interpretation |
|---|---|---|---|
| Open Rate | Percentage of recipients who opened the message | 80% | High open rate indicates effective subject lines and message previews. |
| CTR | Percentage of recipients who clicked on a link | 20% | Low CTR suggests a need to improve call-to-action clarity or message relevance. |
| Time on Message | Average time spent engaging with the message | >60 seconds | High time spent suggests the message is interesting and engaging. |
| Security Awareness Score | Average score on a security awareness quiz | >80% | Improved score indicates enhanced knowledge retention. |
| Behavioral Change | Percentage of users adopting security practices | >15% | Significant change suggests the message is influencing real-world actions. |
Final Wrap-Up
In conclusion, tailored mofu messaging offers a compelling solution to enhance cybersecurity. By leveraging personalized content and targeted delivery methods, organizations can foster a proactive security culture. This approach not only improves user awareness but also strengthens the overall security posture. The effectiveness of tailored messaging hinges on careful consideration of the target audience, clear communication, and continuous evaluation.
This strategy is crucial for mitigating risks in today’s complex threat landscape.